Hi All!
Before starting, I would like to say that, as usual, all the thoughts and info inside this post are my opinions and don’t belong to my company.
Tomorrow will be the day of the public presentation of Windows 10. In this post I would like to say something about some very interested features of the new OS. I think indeed that this release brings a lot of new innovative features (from a Security view-point).

The MS goal was originally to make the new OS one of the most secure version ever released. Have they been able to accomplish this goal? I have made some preliminary tests.
Why a normal user should update?
The most interesting new features are in my opinion the following:
- New Driver Signing Enforcement for UEFI systems with Secure Boot
- A brand-new Kernel Patch Protection implementation (v10 :-))
- Windows Hello (a technology that uses biometrics like your face, iris, or your fingerprint) to launch Windows 10
- Control Flow Guard, and some other new security mitigations
- Implementation of some cryptographic functions directly in Kernel Mode using hardware support
- VSM, aka Virtual Secure Mode – The usage of tiny Virtual Machines to isolate some critical processes (this feature is known even as Device Guard)
- Protected Processes – new light-levels that, used in conjunction with Device Guard, could resist even to Kernel Mode attacks
Two of these points need to be deepen.
First of all I should say something about the new Windows 10 Driver Signing Enforcement. According to the Microsoft post and the OSR articles (1 and 2) all new Windows 10 kernel mode drivers must be submitted to and digitally signed by the Windows Hardware Developer Center (with a Microsoft digital-signature).
This mean that a driver developer (like me) should do 3 things before distribute his kernel software:
- Sign the driver package with his certificate
- Upload the signed driver to MS Hardware Dev Center and agree on some contract details
- Download the new cross signed files (by the owner and MS)
There is a big noise in the Kernel Dev community, even because MS accepts only the submissions that have a valid Extended Validation (“EV”) Code Signing Certificate (that costs a lot), and not the standard code signing certificate.
Even though the process is very cumbersome and intrusive (think about all the small companies and individual developers) it works: a DSE/Patchguard bypass method like the one that I have presented in the last NoSuchCon conference will not work anymore. MS in this way can control even the stolen certificates, and block the loading of drivers signed by bad guys.
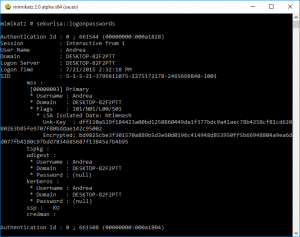
The second feature that I would like to explain is the “Virtual Secure Mode” (aka VSM or Device Guard). VSM is a technology that uses Micro-Vm to isolate some critical (and protected) processes like the LSA Autority process (LSASS.EXE). In this way an attacker, even if he was able to break inside the system, couldn’t obtain the NTLM hash of the login password and can’t attack other network workstation or other applications.
This feature is really powerful (think about the power brought by the isolated protected processes). It is composed by at least 3 kernel modules:
- securekernel.exe – The new Secure Kernel
- skci.dll – Code integrity driver for the Secure Kernel
- cng.sys – The new Next Generation Kernel Cryptography module
The new feature could be enabled ONLY in the Enterprise Edition (see this link) and is incompatible with many drivers (in my personal case the video adapter has started to work with the standard VGA driver when I enabled it).
In summary should you update to the new OS?
In my opinion definitively YES.
The Kernel guys of MS have made an awesome work to raise the bar of the Security of their OS.
The characteristic that I really don’t like is related to the sealing of the OS itself. The enhanced DSE, mixed with Patchguard and Secure Boot technologies make the OS very sealed (like MAC-OS) and limit a lot the power user freedom. But this is a drawback of the equation!
What do you think?
My 2 cents,
Andrea

Hi
what do you think about the recent questions about telemetry and privacy issue? Only FUD or is really a problem?
Thanks