Hi All!
It has been a long time since I have not updated this blog.
As usual a lot of things are going on, and the free time is always very tight 🙂
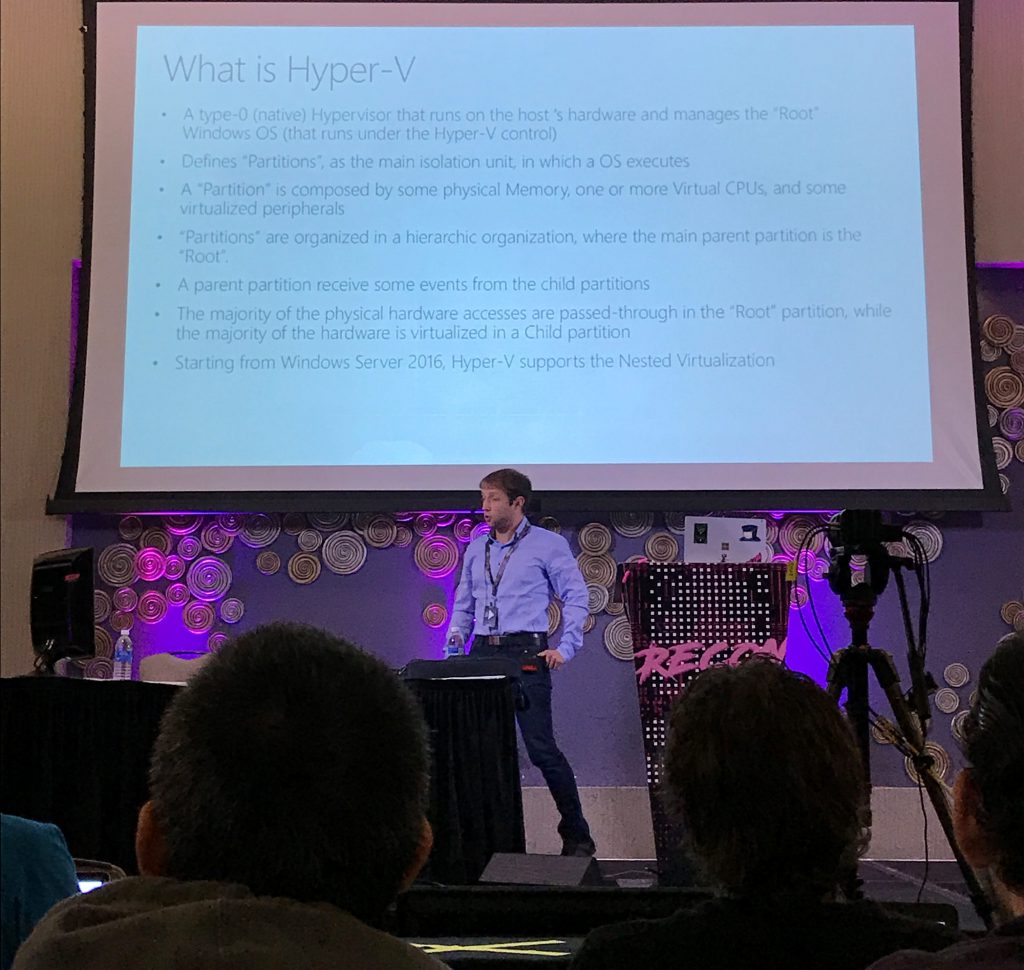
Today I just want to share with my readers the results of my reverse engineering work that I did on HyperV and I have presented in the last edition of the Recon Conference in Montreal.
This edition (May 2017) was quite good, with some interesting talks. We had some good time there, and I have even learnt something.
I presented a talk named “The HyperV Architecture and its Memory Manager”. Apart of my damn English accent, I think that I had some good feedback about the technical level of the talk. I would like to share here the slides:
www.andrea-allievi.com/files/Recon_2017_Montreal_HyperV_public.pptx
I take the occasion even to say that our Intel Processor Driver has been improved. Now it fully supports HyperV Root partitions (this was my demo in the Conference) and runs quite good.
I do not know if I can publish the new source code (I need an approval before), but at the time of this writing I have published the compiled code into our GitHub repository.
https://github.com/intelpt/WindowsIntelPT/tree/master/Compiled_IntelPt
Richard has pinpointed to me some bugs of the IDA plugin and on the driver. I have even improved those.
Few days ago, our friend Alex (@aionescu), has suggested me an interesting reading:
www.cyberark.com/threat-research-blog/ghosthook-bypassing-patchguard-processor-trace-based-hooking/
Basically these guys have done a smart hack with Intel PT, filling a Topa table almost entirely, and setting the Trace by IP…
I am still trying this technique, but potentially it should work. I have only some concern about the timing in which the PMI interrupt will be delivered (this is why it is not considered a threat).
According to the Intel Manual indeed: “This interrupt is not precise, and it is thus likely that writes to the next region will occur by the time the interrupt is taken”
Long story short: Some other tests are needed.
Like a bonus content I would like to show a funny fact:
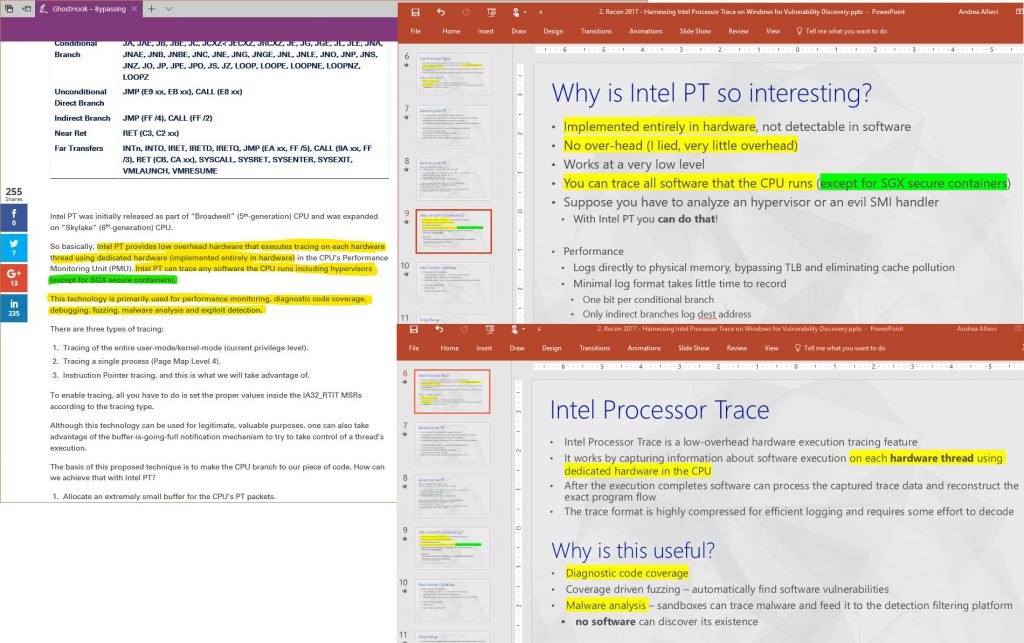
Am I perhaps saying that someone is copying something from someone else? Of course not. This method have been idealized by Cyberark, and uses a “side effect” of the PT PMI Interrupt. The method is original and belongs to them, … but at least THERE IS SOMETHING that is common.
Stay tuned!
Cheers,
Andrea
ps. Again I say that this is my personal blog. I would like to precise that all the impressions, thoughts and information contained here are mine, and not official company statements.